Hackers using spyware made by a little known cyber mercenary company used malicious calendar invites to hack the iPhones of journalists, political opposition figures, and an NGO worker, according to two reports.
Researchers at Microsoft and the digital rights group Citizen Lab analyzed samples of malware they say was created by QuaDream, an Israeli spyware maker that has been reported to develop zero-click exploits — meaning hacking tools that don’t require the target to click on malicious links — for iPhones.
QuaDream has been able to mostly fly under the radar until recently. In 2021, Israeli newspaper Haaretz reported that QuaDream sold its wares to Saudi Arabia. The next year, Reuters reported that QuaDream sold an exploit to hack iPhones that was similar to one provided by NSO Group, and that the company doesn’t operate the spyware, its government customers do — a common practice in the surveillance tech industry.
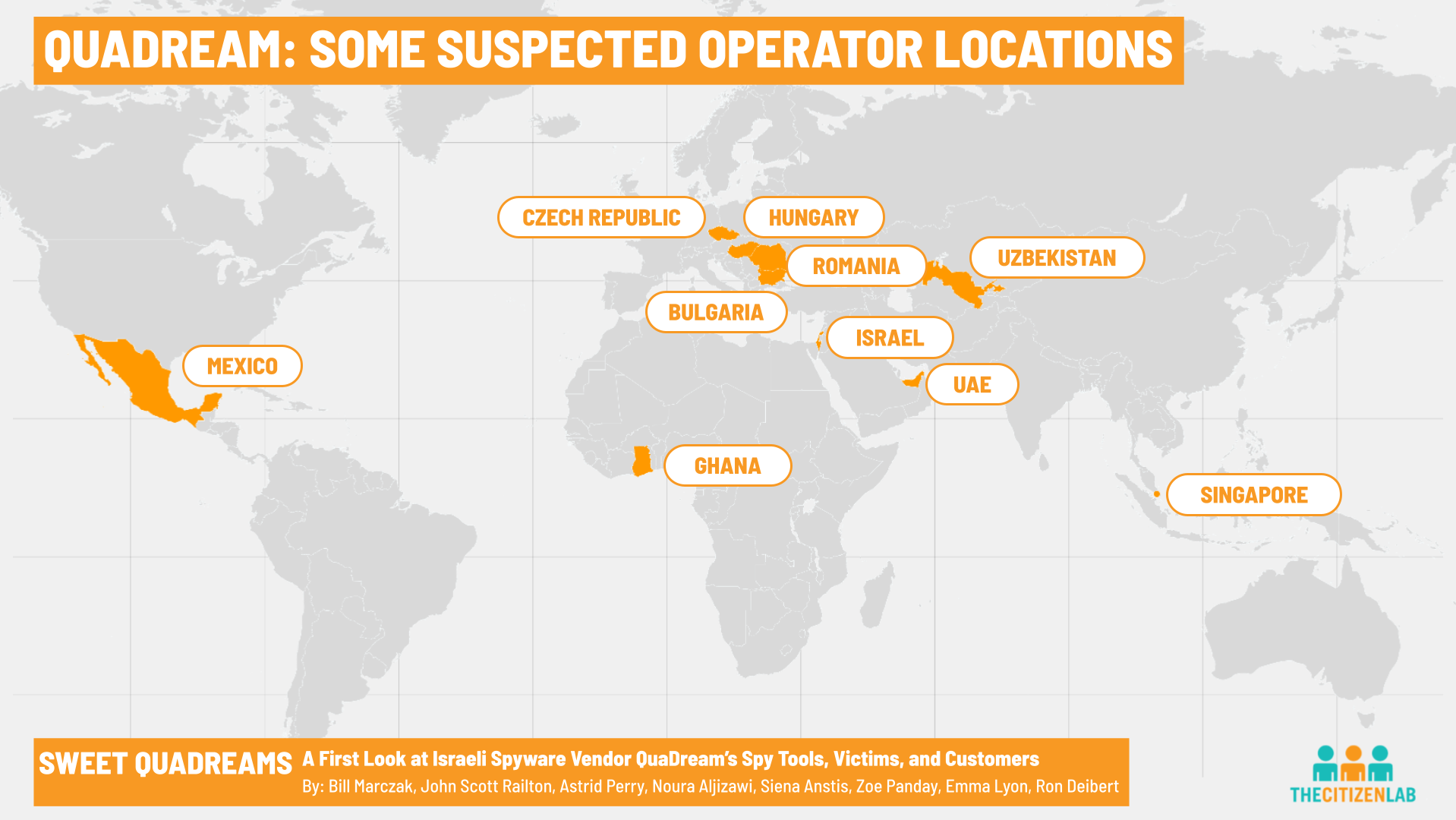
QuaDream’s customers operated servers from several countries around the world: Bulgaria, Czech Republic, Hungary, Romania, Ghana, Israel, Mexico, Singapore, United Arab Emirates (UAE), and Uzbekistan, according to internet scans done by Citizen Lab.
Both Citizen Lab and Microsoft published groundbreaking new technical reports on QuaDream’s alleged spyware on Tuesday.
Microsoft said it found the original malware samples, and then shared them with Citizen Lab’s researchers, who were able to identify more than five victims — an NGO worker, politicians, and journalists — whose iPhones were hacked. The exploit used to hack those targets was developed for iOS 14, and at the time was unpatched and unknown to Apple, making it a so-called zero-day. The government hackers who were equipped with QuaDream’s exploit used malicious calendar invites with dates in the past to deliver the malware, according to Citizen Lab.
Those invites didn’t trigger a notification on the phone, which made them invisible to the target, Bill Marczak, a senior researcher at Citizen Lab who worked on the report, told TechCrunch.
Apple’s spokesperson Scott Radcliffe said that there’s no evidence showing the exploit discovered by Microsoft and Citizen Lab has been used after March 2021, when the company released an update.
Citizen Lab is not naming the victims since they don’t want to be identified. Marczak said that they are all in different countries, which makes it harder for the victims to come out.
“Nobody necessarily wants to be the first one in their community to come out and say, ‘yes, I was targeted,’” he said, adding that it’s usually easier if the victims are all in the same country and part of the same community or group.
Before Microsoft contacted Citizen Lab, Marczak said he and his colleagues had identified several people targeted by an exploit that was similar to the one used by NSO Group customers in 2021, known as FORCEDENTRY. At the time, Marczak and colleagues concluded that those people were targeted with a tool made by another company, not NSO Group.
The analyzed samples include the initial payload, which is designed to then download the actual malware — the second sample — if it’s on the device of the intended target. The final payload records phone calls, record audio using the phone’s microphone surreptitiously, take pictures, steal files, track the person’s granular location, and delete forensic traces of its own existence, among other functionalities, according to Citizen Lab and Microsoft.
Still, Citizen Lab researchers said the malware does leave certain traces that allowed them to track QuaDream’s spyware. The researchers said they don’t want to reveal what these traces are in order to retain their ability to track the malware. They called the traces of malware the “Ectoplasm Factor,” a name that Marzak said was inspired by a quest in the popular game Stardew Valley, which he said he plays.
Citizen Lab researchers also claimed that QuaDream uses a Cyprus-based company called InReach to sell its products.
A person who has worked in the spyware industry confirmed to TechCrunch that QuaDream used InReach “to bypass the Israeli [export] regulator.” For example, the person said, that’s how QuaDream sold to Saudi Arabia.
This workaround, however, apparently didn’t allow them to skirt regulations completely.
“[QuaDream] had four signed deals with countries in Africa (Morocco and few others) but because of the change in the regulation in Israel (limited to only 36 countries), they couldn’t deliver them,” said the person, who asked to remain anonymous to discuss sensitive industry details.
The source said that other than Saudi Arabia, QuaDream also sold to Ghana, the UAE, Uzbekistan, and Singapore, its first customer. Also, the person added, “their system is the most important system in Mexico currently,” it’s operated by the country’s president, and it was nominally sold to the local government of Mexico City, “to keep it quiet.”
The Mexican consulate in New York City did not respond to a request for comment.
According to the source, QuaDream “recently shut down their Android division and is now focusing on iOS only.”
Citizen Lab named several people who allegedly work for QuaDream or InReach. None of them, except for one, responded to a request for comment from TechCrunch. The person who responded said that he has no connection to QuaDream, and that his name was wrongly associated with the company in the past.
The discovery of QuaDream’s malware shows once again that the spyware industry — once dominated by Hacking Team and FinFisher — is not only made of NSO Group but several other companies, most of which are still flying under the radar.
“There’s a broader ecosystem of these companies and targeting individual companies is not necessarily the optimal strategy for reining in the industry,” Marczak said.
In a blog post accompanying Microsoft’s report, Amy Hogan-Burney, the company’s general manager and associate general counsel for cybersecurity policy and protection, wrote that “the explosive growth of private ‘cyber mercenary’ companies poses a threat to democracy and human rights around the world.”
“As the technology industry builds and maintains the majority of what we consider ‘cyberspace,’ we as an industry have a responsibility to limit the harm caused by cyber mercenaries,” wrote Hogan-Burney. “It is only a matter of time before the use of the tools and technologies they sell spread even further. This poses real risk to human rights online, but also to the security and stability of the broader online environment. The services they offer require cyber mercenaries to stockpile vulnerabilities and search for new ways to access networks without authorization. Their actions do not only impact the individual they target, but leave whole networks and products exposed and vulnerable to further attacks. We need to act against this threat before the situation escalates beyond what the technology industry can handle.”
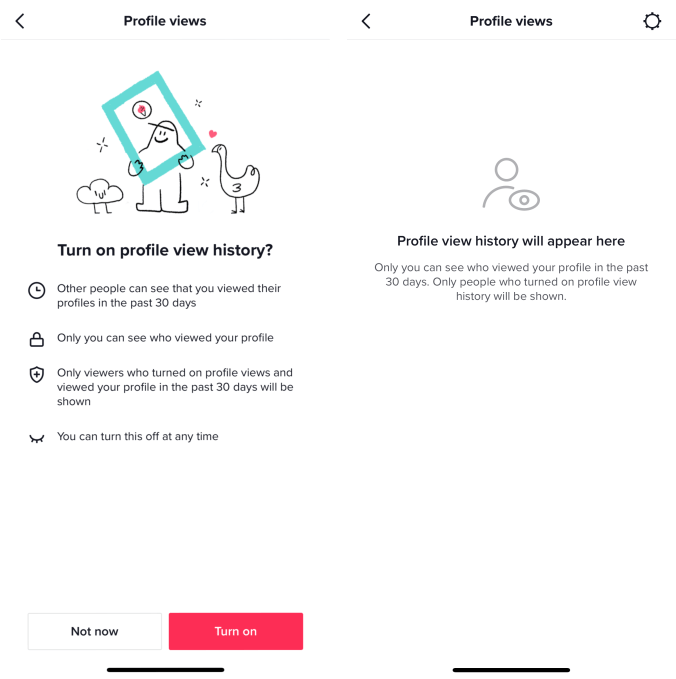
Do you have more information about QuaDream? Or another surveillance tech provider? We’d love to hear from you. You can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, or via Wickr, Telegram and Wire @lorenzofb, or email lorenzo@techcrunch.com. You can also contact TechCrunch via SecureDrop.
Mercenary spyware hacked iPhone victims with rogue calendar invites, researchers say by Lorenzo Franceschi-Bicchierai originally published on TechCrunch








 English (US) ·
English (US) ·