A little-known phone monitoring app called Xnspy has stolen data from tens of thousands of iPhones and Android devices, the majority whose owners are unaware that their data has been compromised.
Xnspy is one of many so-called stalkerware apps sold under the guise of allowing a parent to monitor their child’s activities, but are explicitly marketed for spying on a spouse or domestic partner’s devices without their permission. Its website boasts, “to catch a cheating spouse, you need Xnspy on your side,” and, “Xnspy makes reporting and data extraction simple for you.”
Stalkerware apps, also known as spouseware, are surreptitiously planted by someone with physical access to a person’s phone, bypassing the on-device security protections, and are designed to stay hidden from home screens, which makes them difficult to detect. Once installed, these apps will silently and continually upload the contents of a person’s phone, including their call records, text messages, photos, browsing history and precise location data, allowing the person who planted the app near-complete access to their victim’s data.
But new findings show many stalkerware apps are riddled with security flaws and are exposing the data stolen from victims’ phones. Xnspy is no different.
Security researchers Vangelis Stykas and Felipe Solferini spent months decompiling several known stalkerware apps and analyzing the edges of the networks that the apps send data to. Their research, presented at BSides London this month, identified common and easy to find security flaws in several stalkerware families, including Xnspy, such as credentials and private keys left behind in the code by the developers and broken or nonexistent encryption. In some cases the flaws are exposing the victims’ stolen data, now sitting on someone else’s insecure servers.
During their research, Stykas and Solferini discovered clues and artifacts that identified the individuals behind each operation, but they declined to share details of the vulnerabilities with the stalkerware operators or publicly disclose details about the flaws for fear that doing so would benefit malicious hackers and further harm victims. Stykas and Solferini said that all of the flaws they found are easy to exploit and have likely existed for years.
Others have waded into murkier legal waters by exploiting those easy-to-find vulnerabilities with the apparent aim of exposing stalkerware operations as a form of vigilantism. A huge cache of internal data taken from the servers of TheTruthSpy stalkerware and its affiliate apps and given to TechCrunch earlier this year allowed us to notify thousands of victims whose devices were compromised.
Since our investigation into TheTruthSpy, TechCrunch has obtained further caches of stalkerware data, including from Xnspy, exposing their operations and the individuals who profit from the surveillance.
Xnspy advertises its phone monitoring app for spying on a person’s spouse or domestic partner. Image Credits: TechCrunch (screenshot)
Data seen by TechCrunch shows Xnspy has at least 60,000 victims dating back to 2014, including thousands of newer compromises recorded as recently as 2022. The majority of victims are Android owners, but Xnspy also has data taken from thousands of iPhones.
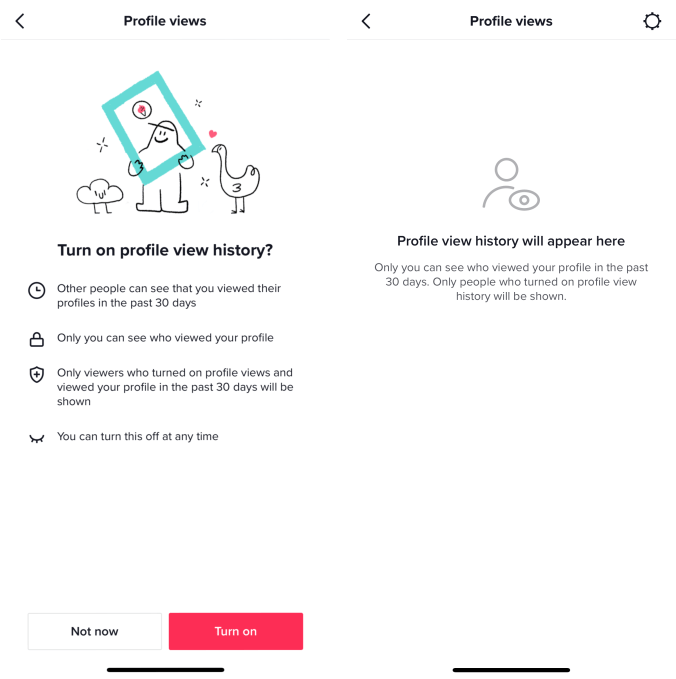
Many stalkerware apps are built for Android since it is easier to plant a malicious app than on an iPhone, which have tighter restrictions on which apps can be installed and what data can be accessed. Instead of planting a malicious app, stalkerware for iPhones tap into a device’s backup stored in Apple’s cloud storage service iCloud.
With a victim’s iCloud credentials, the stalkerware continually downloads the device’s most recent iCloud backup directly from Apple’s servers without the owner’s knowledge. ICloud backups contain the majority of a person’s device data, allowing the stalkerware to steal their messages, photos and other information. Enabling two-factor authentication makes it far more difficult for malicious individuals to compromise a person’s online account.
The data we have seen contains more than 10,000 unique iCloud email addresses and passwords used for accessing a victim’s cloud-stored data, though many of the iCloud accounts are connected to more than one device. Of that number, the data contains more than 6,600 authentication tokens, which had been actively used to exfiltrate victims’ device data from Apple’s cloud, though many had expired. Given the possibility of ongoing risk to victims, TechCrunch provided the list of compromised iCloud credentials to Apple before publication.
The Xnspy data we obtained was unencrypted. It also included information that further unmasked Xnspy’s developers.
Konext is a small development startup in Lahore, Pakistan, manned by a dozen employees, according to its LinkedIn page. The startup’s website says the startup specializes in “bespoke software for businesses that seek all-in-one solutions,” and claims to have built dozens of mobile apps and games.
What Konext doesn’t advertise is that it develops and maintains the Xnspy stalkerware.
The data seen by TechCrunch included a list of names, email addresses and scrambled passwords registered exclusively to Konext developers and employees for accessing internal Xnspy systems.
The cache also includes Xnspy credentials for a third-party payments provider that are tied to the email address of Konext’s lead systems architect, according to his LinkedIn, and who is believed to be the principal developer behind the spyware operation. Other Konext developers used credit cards registered to their own home addresses in Lahore for testing the payment systems used for Xnspy and TrackMyFone, an Xnspy clone also developed by Konext.
Some of Konext’s employees are located in Cyprus, the data shows.
Konext, like other stalkerware developers, makes a concerted effort to conceal its activities and keep the identities of its developers from public view, likely to shield from the legal and reputational risks that come with facilitating covert surveillance on a massive scale. But coding mistakes left behind by Konext’s own developers further link its involvement in developing stalkerware.
TechCrunch found that Konext’s website is hosted on the same dedicated server as the website for TrackMyFone, as well as Serfolet, a Cyprus-based entity with a conspicuously barebones website, which Xnspy says processes refunds on behalf of its customers. No other websites are hosted on the server.
TechCrunch contacted Konext’s lead systems architect by email for comment, both to his Konext and Xnspy email addresses. Instead, a person named Sal, whose Konext email address was also in the data but declined to provide their full name, responded to our email. Sal did not dispute or deny the company’s links to Xnspy in a series of emails with TechCrunch, but declined to comment. When asked about the number of compromised devices, Sal appeared to confirm his company’s involvement, saying in one email that “the figures you quoted don’t match with what we have.” When asked for clarity, Sal did not elaborate.
Xnspy is the latest in a long list of flawed stalkerware apps: mSpy, Mobistealth, Flexispy, Family Orbit, KidsGuard and TheTruthSpy have all exposed or compromised their victims’ data in recent years.
If you or someone you know needs help, the National Domestic Violence Hotline (1-800-799-7233) provides 24/7 free, confidential support to victims of domestic abuse and violence. If you are in an emergency situation, call 911. The Coalition Against Stalkerware also has resources if you think your phone has been compromised by spyware. You can contact this reporter on Signal and WhatsApp at +1 646-755-8849 or zack.whittaker@techcrunch.com by email.
Read more:
- Inside TheTruthSpy, the stalkerware network spying on thousands
- TheTruthSpy exposed: Check if your Android device was compromised
- Your Android phone could have stalkerware, here’s how to remove it
- KidsGuard stalkerware app leaked phone data from thousands of victims
Xnspy stalkerware spied on thousands of iPhones and Android devices by Zack Whittaker originally published on TechCrunch








 English (US) ·
English (US) ·